Gone are those days when computer viruses were primarily written for either fun or to cause minor disturbances. ‘Brain’, the first MS-DOS virus, was launched in 1986, and possibly no one would have thought that this tiny piece of software would evolve into a multi-billion-dollar industry in 2020 and beyond!
Cybersecurity became an interesting topic when the perpetrators started using malicious codes for commercial gains, state terrorism, and cause real harm to either business or even life! This is becoming more and more relevant as digitalization happening across the industry and billions of devices connecting to the internet leaving a wide playing field for malicious users.
If I go by NASSCOM report, we need 10 lakh cyber security professionals in India in 2020. Adding huge cyber security escalations during COVID-19 pandemic, this requirement will surely increase by at least 2 times by 2021! How many trained cyber security professionals do all the training institutes produce in a year in India? A few thousand only!
This is a clear indication and opportunity that we need a structured approach to face this challenge and here are some practical ways to address this huge gap:
- Incorporate cybersecurity curriculum from school level
- Higher education institutes must introduce cyber security courses
- Build cyber security excellence centers with research-oriented facilities
- More intense and outcome driven industry and academia collaboration
- Promote local startups with cyber security product, solution, and services
Often, I see students struggling to find an answer as to what academic degree do they need to pursue a cyber security career. They have a perception that only engineering/science degree are preferred. In fact, anyone with deep passion for cybersecurity with the help of a mentor/coach can truly build a successful career!
To start with, one can follow the pyramid of cybersecurity career (Figure-1) which is based on the philosophy of Sun Tzu’s famous Art of War. The certification, domain, and roles mentioned in Figure-1 should be treated as reference only.
For those who are new to the cybersecurity domain, I would suggest them to go ahead with the fundamentals first, i.e. know your battleground. This is a must-have knowledge that would help you build a solid base and on top of it you can choose any specific domain like Network Security, Cloud Security, OS security, Database Security, Application Security, Secure Software Development, Security Operations, Physical Security, and others to proceed further.
Those who are already into cybersecurity domain and want to advance their career, they have plenty of niche skill-building opportunity and based on their requirement they can pursue various courses and certifications e.g. if someone is working in governance, risk and compliance domain and wants to venture into secure software development domain then he/she needs to go through the secure software development lifecycle course/certification popularly known as DevSecOps along with required coding skills like Python, Java, etc. Similarly, if someone from software development domain wants to build cyber security skills in security compliance domain, then he/she needs to undergo various compliance related training/certification like ISO27001, PCI-DSS, GDPR, etc. and learn how to audit information systems which can be acquired through certifications like CISA by ISACA and association with a mentor (Auditor). I would like to highlight the role of a mentor or a career coach which is inevitable for newcomers. It is very easy to get lost in this vast playing field and this is when mentor helps you to take right decision at the right time. Building a cybersecurity career is challenging and at times daunting due to time, effort and money you need to invest for training, certification etc. so it is prudent to get a mentor from the industry who can make your journey successful.
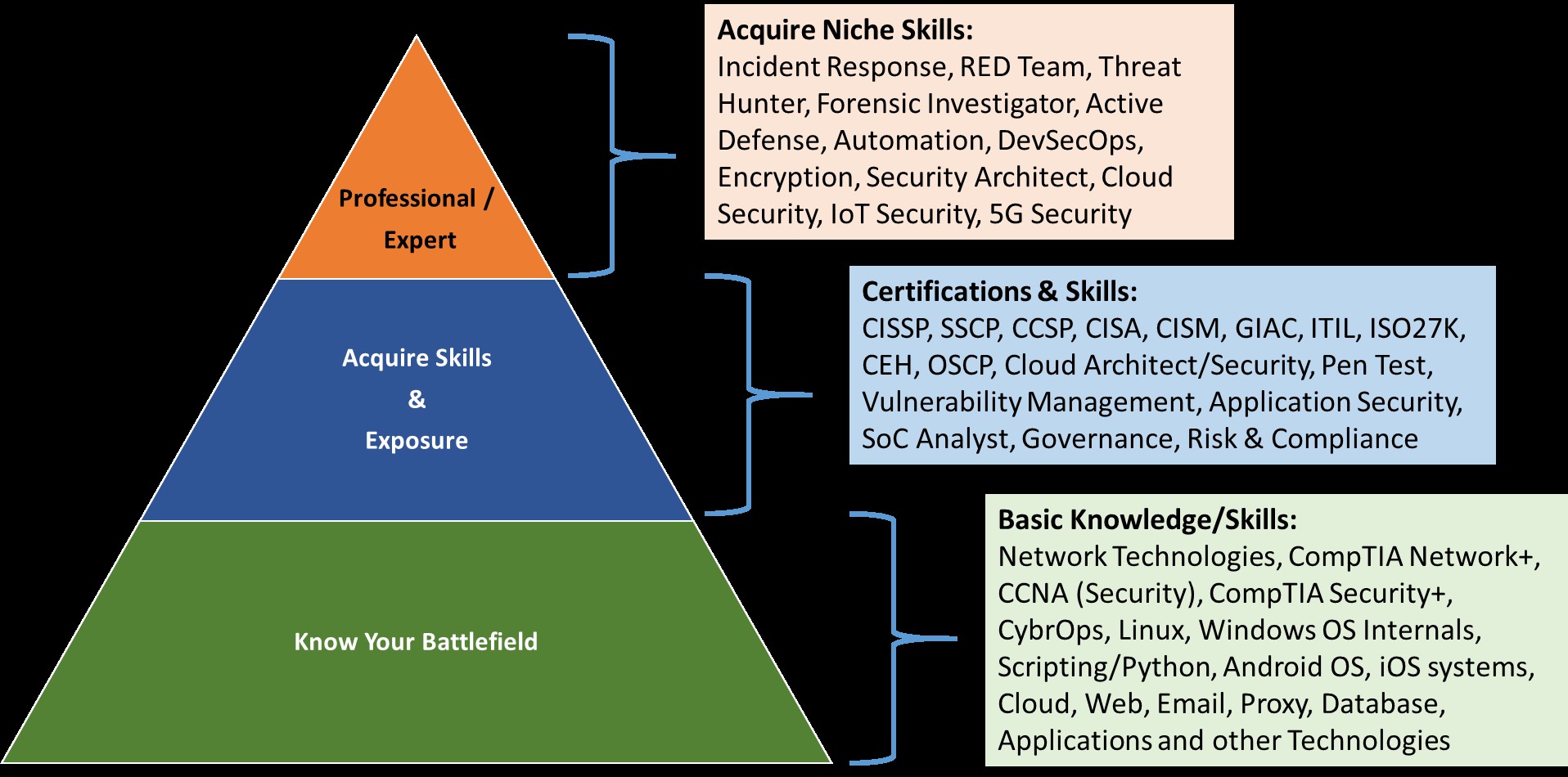
When you reach the 3rd layer of the pyramid, there is a possibility that the priorities have already been shifted either from business side or your own goals and this is perfectly normal considering the rapid volatility in the industry. This is when one question becomes so important, which domain to focus? Simply, search for cybersecurity job openings and look for skills organizations are looking for, do some analysis and find your path. This will put you into two challenges though,
- You might need to upgrade your skill through training / certification,
- Look for a change if your current organization doesn’t have that role!
Either way, progress is the only choice. Here is the list of most relevant cyber security career tracks as of Sept. 2020. This list is not in order of preference and all have equal weightage.
- Governance, Risk and Compliance Professional – The GRC professionals ensures that the organization is managing risks, internal controls, and key compliance requirements to maintain appropriate governance and produce business results. Certifications like Governance Risk and Compliance Professional (GRCP), Certified in the Governance of Enterprise IT (CGEIT), Certified in Risk and Information Security Control (CRISK), IT Infrastructure Library (ITIL) Expert, Certification in Risk Management Assurance (CRMA), PMI Risk Management Professional (PMI-RMP) etc. shall help build your competence but you need get your hands dirty to sharpen your GRC skills.
- Cyber Forensic Professional – This domain has grown very fast during last few years due to increased cyber security incidents across private and public organizations. One of the key deliverables from cyber forensic expert is to collect chain of evidences which is acceptable to the court of law so that perpetrators can be brought to justice. Certifications like Certified Forensic Computer Examiner (CFCE), Certified Computer Examiner (CCE), GIAC Certified Forensic Analyst (GCFA), GIAC Certified Forensic Examiner (GCFE) etc. shall help you acquire reasonably good understanding. Like other domains, this requires huge hands-on exposure to become expert in this field.
- IOT Security Professional – Internet of Things (IOT) is now a reality and it is growing faster then anticipated. This domain brings unique security challenges and to control these, a new approach is required hence a very promising domain for building capabilities. There are very few training and certifications worth mentioning here, however, early adopters will certainly gain. Some platform service providers provide training on IOT security like Microsoft, Amazon, Attify etc.
- Security Operation Professional – Security Operation (SecOps) is the nerve center of any organization. It brings real-time visibility, detects, manages, responses and remediates security incidents. It requires multiple different skill set to make SecOps successful in an organization. Some of the skills required are Incident Response, Threat Analyst, Threat Hunter, SecOps Manager, and Security Engineer. All these skills have their own training and certifications e.g. GIAC Certified Incident Handler (GCIH), EC Council Certified Incident Handler (E|CIH), GIAC Certified Threat Intelligence (GCTI), GIAC Network Forensic Analyst (GNFA).
- Cloud Security Professional – Cloud technologies will continue to evolve rapidly and in the recent past, the cloud adoption has increased multiple times proving its worth and sustained relevance. The difficult part is to remain relevant in this dynamically changing environment! Some cloud certifications are obviously coming from the respective OEMs e.g. AWS, Google and Microsoft and apart from this, Certified Cloud Security Professional (CCSP), Certificate of Cloud Security Knowledge (CCSK), CompTIA Cloud+ etc. are also keep you up-to-date.
- Application Security professional – Entire computing run on various types of applications i.e. Web Apps, Database Apps, Messaging Apps, E-comm apps, Payment apps, AV apps and you name it. It is important that all applications should be developed with security from ground up and to ensure this, organizations have already adopted various framework and controls. Few such framework are DevSecOps and Site Reliability engineering (SRE). One need to have software development background to gain footage in Application security domain though there are some trainings and certifications that will certainly help e.g. EC Council Certified Application Security Engineer (CASE), Certified Secure Software Lifecycle Professional (CSSLP), GIAC Certified Web Application Defender (GWEB).
- Information Security Auditor – This is a niche skill which not only require information security domain knowledge but also one’s observation and auditing skills. The demand for information security auditors is growing since the growth of security controls, security incidents, regulations from various statutory and regulatory bodies. There are various auditor training and certification programs to help you start your career e.g. ISO 27001 Lead Auditor, PCI-DSS Auditor, GDPR Lead Auditor, Certified Information Systems Auditor (CISA), British Standard Institute, India (BSI) etc.
- RED Team / Pen Tester / Ethical Hacker – For simplicity, I have converged all the three terms together though in practice they have few differences. Organizations need to ensure that they are secure and prove the same by hiring / performing hacking exercises into their systems so that they can detect vulnerabilities early and patch those before real attackers exploit them. This is when they need RED team, Pen testers and ethical hackers. Some certifications like EC Council Certified Ethical Hacker (CEH), Offensive Security Certified Professional (OSCP), GIAC Penetration Tester (GPEN).
Here comes the next question, where do I get training for these courses/certifications?
When I started my security career back in 2000, the nearest cyber security training institute was in the US! But fortunately, we have many training institutes now and that makes our life tougher because I don’t know why and which institute is suitable for me. Every training institute is delivering something which shall help you in some way but when it comes to career investment, it is advisable that you do good amount of research before you bet your hard-earned money into this. Here are few guidelines which shall provide you with some research cues.
-
- Course Content – Collect the course syllabus/content and check if these contents are contemporary and employers are asking for these skills
- Infrastructure – The Institute must have adequate and right infrastructure to impart the required training e.g. digital classrooms, good quality laptops/Desktops, remote training facilities, digital library, breakout area, anywhere lab etc.
- Faculty – This is probably the most important aspect of any training. A good training institute must engage faculty from industry on a regular basis apart from academic faculties. Faculties from industry brings diverse knowledge and skills which will benefit students.
- State-of-art lab – Lab is the place where you will make mistakes and start learning so it is important that the institute must have an up-to-date lab with all software, hardware and accessibility. The lab can be in the cloud as well and this will make your training more flexible and enjoyable.
- Availability of specialization – The institute must have areas of specialization and should provide relevant training, lab and faculty. These courses are specially required for experienced and advance cyber security practitioners.
- Feedback – Talk to the existing students and get their experience, however, remember that feedback may vary depending on their experience and expectations. It is better that you talk to a successful candidate who have passed out of that institute.
To summarize, when you are starting your cyber security career journey consider the following:
To start the journey, you need to have passion for cyber security which will be your driving force. During the journey, acquire relevant skills through right training/certification and to make your journey successful and sustainable, never stop learning. I would like to end this blog by mentioning one of my favorite quotes from Alvin Toffler…
“The illiterates of the 21st century will not be those who cannot read and write, but those who cannot Learn, Unlearn and Relearn”
References:
NASSCOM Cyber Security Skill Gap Report –
https://nasscom.in/sites/default/files/FutureSkills_An_Industry_Response.pdf
https://www.bsigroup.com/en-GB/industries-and-sectors/ICT-and-telecoms/
https://www.offensive-security.com/
https://www.comptia.org/certifications/security
https://www.oceg.org/certifications/grc-professional-certification/
https://www.oceg.org/certifications/grc-professional-certification/


 6 Sep 2021
6 Sep 2021



